JC’s Cybersecurity News & Notes – July 2020
Hello friend, thank you for tuning into my Cybersecurity News section at jcutrer.com. This section is an experiment. I keep a close eye on the latest developments in Information Security and this is a place for me to take notes and link to notable news, articles, and reports.
Let me know what you think about the content. I will update this article throughout the month with noteworthy InfoSec stories but don’t expect updates every single day. Cheers!
Updated: 7/15/2020
Microsoft patches wormable RCE in Windows DNS server
With a CVE score of 10.0, this patch should be applied immediately! You are STILL vulnerable even if your DNS service is not publicly accessible.
Workaround
The following registry modification has been identified as a workaround for this vulnerability. HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\DNS\Parameters DWORD = TcpReceivePacketSize Value = 0xFF00
Note: A restart of the DNS Service is required to take effect.
Link: Microsoft
Twilio will require two-factor auth for all customers
Twilio customers using paid accounts (excluding trial accounts) will be required to setup 2FA starting October 12, 2020
Link: Twilio
Detect and Remediate Illicit Consent Grants in Office 365
Microsoft seems to be acting on the highly publicized issues with Office 365’s rash of malicious 3rd parts apps connecting to customer’s domain via OAuth.
This is Microsoft’s guide to detecting and removing these rogue authorization.
Link: Microsoft
Google Releases Tsunami Security Scanner
Tsunami is a vulnerability scanner written in Java. It was originally written for internal security scans at Google. The code scanner and plugins live in two separate GitHub repos.
https://github.com/google/tsunami-security-scanner
https://github.com/google/tsunami-security-scanner-plugins
Microsoft seizes domains and puts a dent in business email compromise (BEC) abuse on it’s Office 365 platform.
Here are the domains listed in the court order
- mailitdaemon[.]com
- officemtr[.]com
- officesuited[.]com
- officehnoc[.]com
- officesuitesoft[.]com
- officeinventorys[.]com
Link: https://threatpost.com/microsoft-seizes-domains-office-365-phishing-scam/157261/
Video: Advanced VirusTotal Tutorial
VirusTotal is one of the most used cybersecurity tools by users and researchers alike. This video from The PC Security Channel on YouTube discusses how to use VirusTotal as a cybersecurity professional to get a deeper insight into threats.
Link: YouTube
Microsoft announces Project Freta
Project Freta is a virtual machine memory analysis tools. The goal of the project is to detect rootkits and stealthy malware by looking for anomalies in memory snapshops.
Currently, the tool is free to use and will read the following memory dump file formats and generate a detailed report.
Supported types:
- Elf Core Dump of Physical Memory (.core)
- LiME image (.lime)
- Raw Physical Memory Dump (.raw)
- Hyper-V Memory Snapshot (.vmrs)
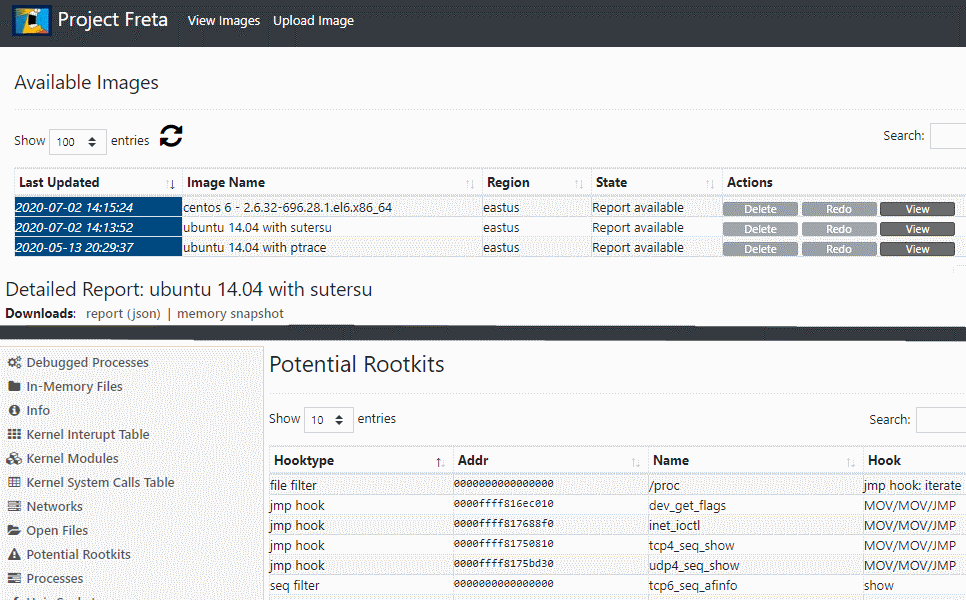
As Freta matures it will likely be rolled into Azure Security Center or used at scale to detect malware across Azure VMs.
Link: Microsoft Research Blog | Freta Portal
Malicious code extraction and deobfuscation tutorial video
In this video tutorial, Scott Nusbaum of TrustedSec walks us through the process of deobuscating malicious code found in a malware sample.
Links: TrustedSec blog | YouTube
No magic wand for business email compromise (BEC)
Excellent interview with Proofpoint’s EVP of Cybersecurity Strategy, Ryan Kalember. Ryan describes in detail some of the ways cybercriminals are leveraging Azure Apps for Office 365 to run their stealthy BEC campaigns.
Patrick Gray points out the vulnerable position Microsoft leaves it’s Office 365 customers in when they don’t pay for expensive Azure AD P1 licenses.
Link: RISKY.BIZ
07/03/2020
NSA releases best practices for securing IPSec Virtual Private Networks
The document describes what encryption and hashing algorithms you should using and gives VPN configuration examples for multiple firewall vendors.
Recommended minimum ISAKMP/IKE settings
- Diffie-Hellman Group: 16 or 20
- Encryption: AES-256
- Hash: SHA-384
Minimum IPSec Policy
- Encryption: AES-256
- Hash: SHA-384
- Block Cipher Mode: CBC
Link: NSA
Alina POS malware exfiltrates cardholder data via DNS queries
Example query
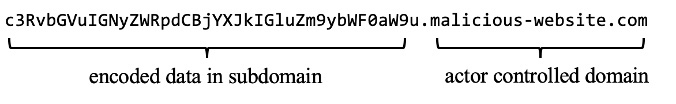
The malware will attempt to query the following 4 domains to transmit stolen data. Sinkhole these domains in your DNS servers.
- analytics-akadns[.]com
- akamai-analytics[.]com
- akamai-information[.]com
- akamai-technologies[.]com
Researchers have found that the malware author has used this technique as far back as 2018.
Link: Black Lotus Labs
Firefox 78 has now killed off both TLS 1.0 and TLS 1.1
Mozilla, Google, Apple and Microsoft have committed to disabling TLS 1.0 and TLS 1.1 by the end of this year.
Here is the error you will see when visiting a website that only supports TLS 1.0 or TLS 1.1 in Firefox 78.
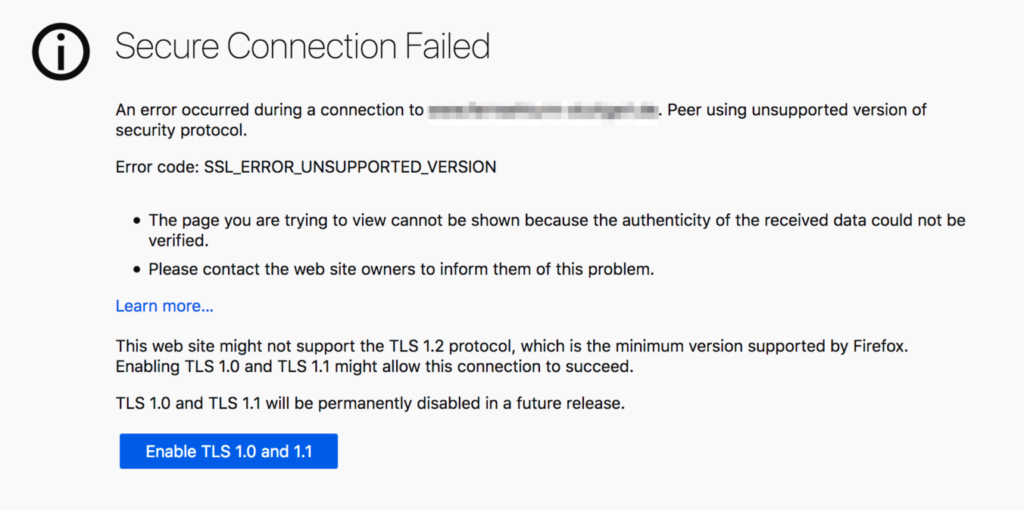
Links: Mozilla | Naked Security
In the wake of COVID-19, EFF profiles invasive employee monitoring (bossware) software
Companies are beginning to tract remote workers with a multitude of spy tools, sometimes referred to as Bossware.
Some of the software profiled allow employers to tract GPS location, take chronological screenshots of the desktop and even covertly activate the webcam and microphone.
Here is a list of software profiled in the study…
- Interguard
- StaffCop
- CleverControl
- Crossover WorkSmart
- Teramind
- Time Doctor
- ActivTrak
- DeskTime
- Hubstaff
- WorkPuls
- Work Examiner
Link: EFF
Microsoft Releases out-of-band Emergency Security Updates for Windows 10, Server 2019
CVE-2020-1425 is a remote code execution vulnerability in the HEVC codec plugin installed from the Microsoft Store. With a CVSS score of 7.3, this vulnerability has a rating of Critical. The HEVC codec library is not installed by default on Windows 10.
CVE-2020-1457 is a related remote code execution vulnerability with a rating of Important.
Links: Threatpost | CISA
Thanks for reading Cybersecurity News at jcutrer.com. Did you find this page insightful? Let me know in the comments section below.